Welcome back to our Triage Thursday™ blog series, where we summarise all the updates and changes made to Triage over the last week. In the news today:
- Small fix for the Emotet configuration extractor
- Updated configuration extractor for a new Vidar variant
- New signatures for Luca stealer
- New signatures and configuration extractor for Arrow RAT
- New signatures for Dracarys Android spyware
- New signatures for Yanluowang ransomware
- New configuration extractor for Loaderbot
- Added improved general detections for cryptominers
- New signatures for Gost tunneling tool
As always if you have any feedback, questions or issues about Triage™ feel free to reach out to us any time - knowing what is important to our customers and users is very helpful in such a rapidly changing environment. You can reach us directly through the website, on Twitter, or using the Feedback option on an analysis report page.
Not signed up yet? Head over to tria.ge to register for a free account.
Luca Stealer
Luca is a stealer written in the Rust programming language and first identified in July 2022 by the team at Cyble. The source code seems to have been deliberately made public through underground forums by the developer for unclear reasons (Cyble suggests to build reputation since they seem to have no prior presence), and since then a growing number of instances of the malware have been spotted in the wild. It is also now listed on Github where the original creator seems to be continuing to work on it with multiple updates seen since the initial version, expanding the functionality each time.
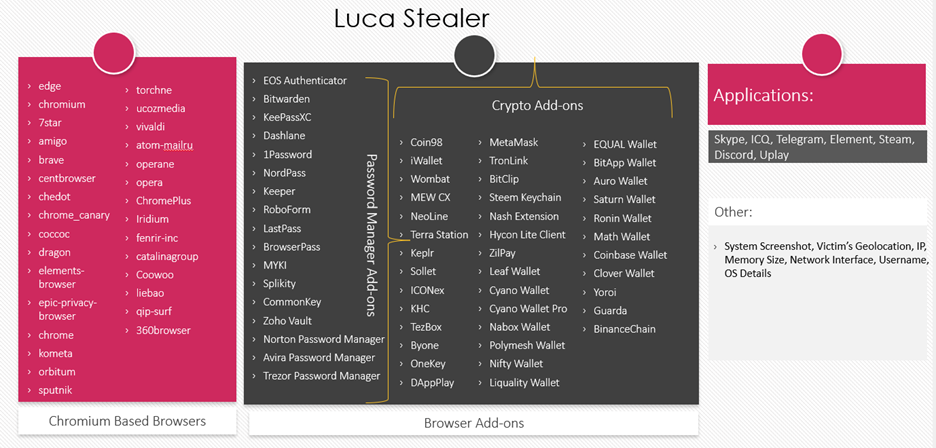
The following image from Cyble’s analysis shows the main features of the stealer - in general its targets are pretty familiar, going after browser data and cryptocurrency wallets. The password managers are a little less common:
We’ve reviewed the samples shared so far and have built out initial detections for the family, and will be keeping an eye open as usual for any new updates.
Analyses:
Arrow RAT
Arrow was first reported by Cyjax towards the end of 2021, after it was spotted being advertised on underground forums:
As described it is available as a service, purchasable by anyone to use in their own campaigns. It’s features are generally fairly typical of a RAT, with its most notable aspect being the hVNC module which basically gives an attacker full remote access with minimal need for technical knowledge to use it.
We’ve identified quite a few samples of the family so we have built out detections and a configuration extractor which can dump the C2 information, botnet ID, and the mutex name used to prevent the family from reinfecting an already compromised device.
Analyses:
Dracarys Android Spyware
At the start of this month Meta published their threat report for Q2, covering the main risks they see across the company. In this they cover a family called Dracarys which is a new Android stealer/spyware which is being used by an APT group called Bitter (aka T-APT-17). This team generally targets countries in South East Asia and has been active since 2013.
Dracarys is spread by trojanizing legitimate applications like Signal, Telegram and Whatsapp; using the brand recognition to encourage people to accept the permissions requirements since all of these have reasonable explanations for accessing call information, text messages, cameras, etc. Like most similar Android trojans the family abuses the accessibility services to automatically click through some UI options, grant itself permissions, etc.
We have limited public samples available currently but have built some initial detections, and as usual will update as/if needed.
Analysis:
Yanluowang Ransomware
This month a little company called Cisco announced that it had been breached by a ransomware gang back in May 2022, who had tried to extort them with threats of leaking files openly on the internet. Samples from this attack have not been made public at this stage but this incident prompted us to look into the group and add detections for the family based on previous samples that are openly available.
As a ransomware the family is not new, with the first references going back to a Symantec Threat Hunter Team blogpost in October 2021. Later in the year TrendMicro also published analysis, observing that a new version had appeared that was legitimately code-signed to lower detection rates, and appeared to have added some ways to more fully encrypt corporate/production environments by stopping processes related to database and backup management.
The malware seems to be designed for targeted attacks where the users already have access in some form, as TrendMicro observe that it requires specific parameters to be provided in order to run properly which would not be practical if they were relying on the user triggering it.
Analyses:
LoaderBot
LoaderBot is a single-stage loader which is used to download and deploy other malware families. It was first reported by the researcher benkow_ back in 2018, when they analysed several different families created and sold online by the same developer. It’s fairly straightforward in terms of features but is quite capable of doing its job - its only significant evasion techniques seem to be that it will exit if it detects some tools like Task Manager or Process Hacker being run on the system.
In 2020 it was reported that the original creator had been arrested in Russia after his malware was used in attacks within the country. Despite this though we’ve been seeing quite a few samples appearing on the public cloud in recent months so we decided to add detections.
Analyses:
Gost
Gost is a ’legitimate’ network tunneling tool written in Golang and openly available through Github. It supports a number of different protocols and evasion techniques to enable stealthy communications and data exfiltration for use in pentesting/red team exercises, but of course this can also be easily abused by malware creators for their C2 operations. You can find the readme with more technical details on Github here.
Although it is not technically malware we decided it’s certainly something worth reporting if present in an analysis, so we have implemented detections and given it a family tag for easy reference.
Analyses:
