Welcome to another week of Triage Thursday™ updates! It’s been another fairly quiet week here as we work on upcoming features, but as usual we have a few changes to go over.
- New Search tags for VM operating system
- Anchor_DNS Backdoor signatures
- XLoader family detection
- Buer Loader updates
- Suncrypt Ransomware update
We have also been taking a close look at recent ZLoader samples, and are planning to release a blogpost going over these samples next week. Keep an eye here and on our [social media] to catch that.
If you have any feedback on Triage™ or particular samples please do get in touch! You can reach us directly through the website, on Twitter, or using the Feedback option on an analysis report page.
Not signed up yet? Head over to tria.ge to register for a free account.
Platform Search Tags
We’re continuing to look for ways to improve Triage’s Search feature, and this week have pushed another minor update which enables filtering by target platform.
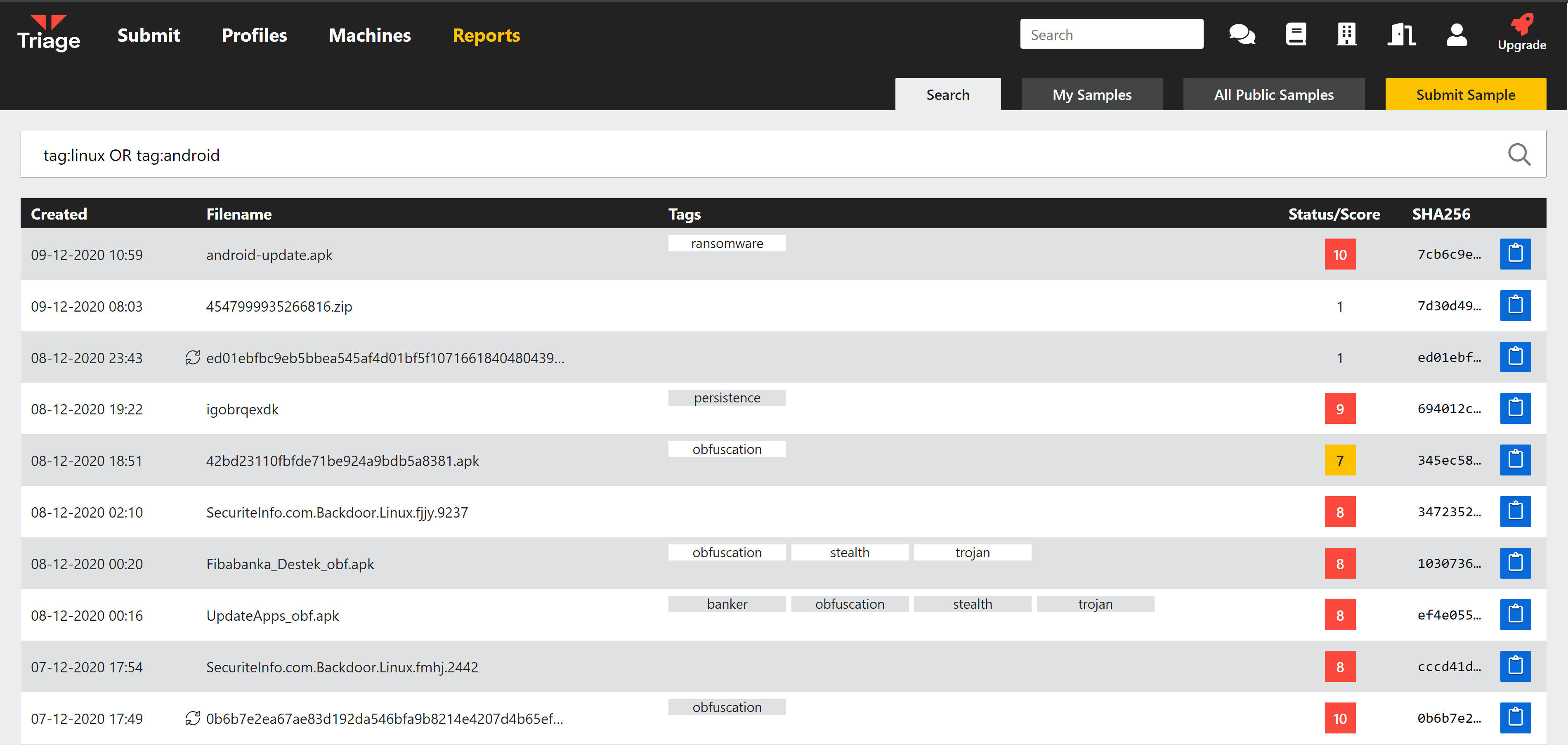
Just use the new terms tag:linux or tag:android in Search.
Anchor DNS
Anchor_DNS is a backdoor/trojan created by the group which also develops Trickbot. It was first reported towards the end of 2019 and has been active throughout 2020, although at a much smaller scale than the main Trickbot payloads. It has been reported to only be deployed on certain high-profile targets compromised by Trickbot campaigns, acting as a remote backdoor for the attackers to manually deploy additional payloads and modules.
The backdoor gets its name from the use of DNS tunnelling to carry out its C2 communications, which is intended to help it go undetected on an infected network.
In mid-2020 it was reported that the family had gone multiplatform, with a Linux variant being seen in the wild.
We have examined available samples and implemented static detection for Linux and Windows variants of the family. As with the main Trickbot payload, Anchor_DNS regularly receives new versions and we will update detections as needed in the future.
Analyses:
XLoader
It was recently reported by @KrabsOnSecurity that the Formbook stealer has rebranded to XLoader, although the majority of the payload itself remains the same as before.
For those not familiar with the Formbook family, it is a strain of infostealers which have been operated as a service since at least 2016. The family generally includes significant anti-VM and anti-analysis techniques which can make it difficult to reliably analyse in a sandbox environment.
We have examined the new samples, and implemented some initial signatures to differentiate between the 2 variants. Currently some will still receive the Formbook family tag alongside XLoader but this will be fixed in a future update.
Some samples are listed below, but as usual you can find additional submissions using the search family:xloader.
Analyses:
Buer Loader
Buer is a loader framework which was first reported in late 2019, sold through forums for use with various payloads. We implemented detection for it back in October, but recently observed a variant which had some improvements over earlier versions and was evading our signatures.
The main change we observed on close inspection was that the original persistence mechanism had been replaced with a stealthier version. We have now updated static detection to cover this variant.
Analyses:
Suncrypt Ransomware
SunCrypt is a ransomware family which appeared in October 2019 but has mainly been active through the 2nd half of 2020. As we mentioned in a previous blogpost, it has found some success against organisations such as University Hospital New Jersey and a school district in North Carolina. Since then CyWare have reported that during the breach of an unnamed organisation the SunCrypt operators also carried out a DDoS attack after the ransomware had infected the network, using it as extra leverage to force payment of the ransom.
We recently observed a sample which wasn’t detected by our signatures. We have updated to fix this, but have so far only observed one such sample to test with. We will keep an eye open for future updates and make changes as required.
Analysis:
