Welcome to another Triage Thursday™ blogpost, where we look at the recent updates to the sandbox and its detections. Today we’ve got a couple of weeks of changes since we didn’t have time to put out a post last week, so let’s get straight to it:
- Updated configuration extractor for new Eternity samples
- Added Linux detections for Lightning framework
- Added signatures for Revive Android banker
- Added signatures for Spynote Android RAT
- New configuration extractor for XtremeRAT
- Added new signatures for Gootloader
- Added support for new Lockbit ransomnote format
In addition to the specific family updates this week the team have also been starting a review of our general Linux behavioural signatures to flesh those out and cover more suspicious actions. You will see a few new ones already appearing in reports, and we’re aiming to continue working on that in the background to make further improvements.
As always if you have any feedback, questions or issues about Triage™ feel free to reach out to us any time - knowing what is important to our customers and users is very helpful in such a rapidly changing environment. You can reach us directly through the website, on Twitter, or using the Feedback option on an analysis report page.
Not signed up yet? Head over to tria.ge to register for a free account.
Eternity
We initially covered the Eternity project back in June this year when we added detections for the modules that we had come across. If you missed that blogpost the family is a recent malware-as-a-service offering which aims to give a lot of flexibility to its users - instead of focusing on just 1 type of malware Eternity has a number of different modules including an infostealer, cryptocurrency miner, clipper stealer, a fully featured ransomware, and a worm spreader. Each is sold separately and buyers can customise their own specific payload via a Telegram bot which requires no technical knowledge to use.
The framework seems to be in active development, and this week we’ve updated our configuration extractor to properly handle a new encryption algorithm seen in the latest samples. The algorithm change is fairly straightforward - it appears to have just switched from using a mix of base64 and AES to simple XOR-based encryption.
Analysis:
Lightning Framework
A few weeks ago Intezer published a blogpost about a new Linux-based malware framework that was seeing poor detection across the board. Named Lightning, it is an advanced threat with a highly modular design that can install different types of rootkit and deliver custom plugins. It’s also reported to have quite complex communication methods with the C2 infrastructure with a few different options for both active and passive approaches depending on stealth requirements.
Check out Intezer’s blogpost linked above for a comprehensive technical breakdown of the available modules and their functionality.
The samples available currently are limited and do not include all aspects of the malware, but we’ve reviewed the files we can get our hands on and have implemented some initial detections. As always we’ll revisit the family if/when needed to keep it up to date.
Analyses:
Revive Android Banker
Revive is a new Android banking trojan first discovered in June 2022 by the team at Cleafy - their report on it is available here. Currently it is more targeted than most bankers, only going after users of the BBVA bank in Spain, but the base functionality it uses is still very familiar from other Android threats. The versions reported by Cleafy impersonate a legitimate 2FA app from the bank and heavily base their lures around that brand but this may change and expand as the family develops past these initial versions.
Under the hood we see the same techniques used by most other Android bankers - especially abuse of the Accessibility Services to log all keystrokes and intercept text messages to/from the device. This allows them to bypass the 2FA implementation by acquiring the original credentials and intercepting the one-time password that is then sent out via SMS.
Cleafy suggest this could just be early days for the new family so we may have to revisit in future, but for now we have reviewed some samples and implemented detection.
Analysis:
SpyNote Android RAT
SpyNote is an older Android threat, going back to at least 2016 when it popped up imitating legitimate paid apps to try and convince users to install the ‘free’ version from non-Google Play sources. In 2020 it came back into focus after researchers at Lookout identified a surveillance campaign seemingly being run by the Syrian Electronic Army (a state-sponsored group) against targets in Syria.
The malware has a range of features including:
- Extraction of contact information
- Remote access to the device’s microphone and camera
- GPS tracking
- Deploy additional payloads
- Exfiltrate files from the device to C2
- Dump out device info like carrier details, IMEI number, etc.
Unlike some of its contemporaries SpyNote does not seem to try and get itself listed on the Google Play store, instead relying on users to sideload it from 3rd party sources. We have analysed a number of available samples and implemented initial detections.
Analyses:
XtremeRAT
XtremeRAT is stealer family which is thought to have first appeared around 2010. Written in Delphi, it shares sections of its code base with some other families which popped up around the same time such as SpyNet, Cerberus and Cybergate.
It is a fairly standard stealer with functionality you’d generally expect from this kind of family:
- Direct interaction with infected systems via remote shell
- Upload or download files
- Terminate running processes and services
- Capture screenshots
- Record audio and/or video from connected webcams and microphones
A detailed analysis of the family can be found in Mandiant’s 2014 blogpost about it available here.
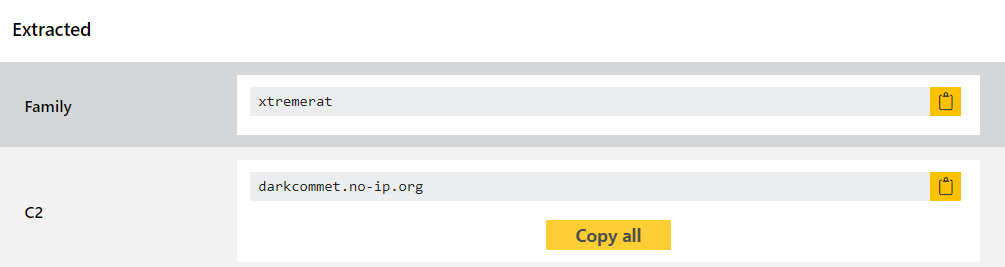
We added detections for the family last year, but this week we revisited it to include a full configuration extractor to dump the hardcoded C2 domains.
Analyses:
Gootloader
Gootloader is a multi-stage dropper built in Javascript which has been around since late 2020. Its early versions deployed their own end payload called Gootkit from which the loader took its name, but since then the actors have diversified to start delivering other families primarily. The ‘multi-stage’ part refers to the family splitting the infection process up into small modules to make detection harder, and this is augmented by the fact the family loads these modules directly into memory to limit artifacts on the disk which might be picked up.
The family went quiet for a while after many defenders started using some open-source tooling to quickly decrypt the malware and easily detect it. However in mid-2022 it has appeared in the wild again with a new version that gets around this detection method, and campaigns dropping things like CobaltStrike have begun to be seen.
We’ve had signatures and a configuration extractor for Gootkit, the initial payload, for a couple of years now but had not added specific detections for the loader since the 2 traditionally came as a package. However with that changing, and a new version starting to appear again, we have revisited it to add new detections based on the available samples.
Analyses:
