Welcome back to another week of Triage Thursday™ update news! We’ve got a few updates to signatures and configuration extractors to introduce today:
- Added configuration extractor for DJVU ransomware
- New family signatures for NGLite RAT
- Updated Vidar detections for new C2 services
- Tweaked CobaltStrike handling
We also have an update to the Triage website itself, with new ways to register for and login to your accounts. Read on below for more information on using your Google or Github accounts to access Triage!
As always if you have any feedback about the platform or the samples uploaded there please do get in touch! You can reach us directly through the website, on Twitter, or using the Feedback option on an analysis report page.
Not signed up yet? Head over to tria.ge to register for a free account, or reach out to us using the contact form on our website to find out more about our commercial options.
Login to Triage via Google and Github
Single Sign On (SSO) is a great way to make accessing web services easier and less painful than having to remember or store passwords for every website you use. When you’re working with multiple tools it can be much quicker to just login once, and for organisations SSO can also be a useful way to increase security via centralised policies regarding session timeout or password strength.
As such, we have today released support for 2 major identity providers - Google and Github. You can now register for a Triage account using either service and login without the need for a dedicated username/password combination.
If you’ve already registered an account with an email address, you can switch to logging in via SSO anytime as long as the email address matches that of your Google or Github account.
For our Enterprise customers, we are working on SAML support which should be available in the next few weeks. Watch this space!
How to unlink a Google or Github account from Triage
If you’ve registered an account via SSO but then want to remove that link, all you have to do is logout of your account and use the Can't login? option to reset your password. Once done, you can access the site with the standard email address/password combination.
DJVU Ransomware
This week we have revisited the DJVU ransomware family to add a dedicated configuration extractor. This augments our existing detections for the family based around ransomnote dumping and behavioural signatures, and should provide more reliable coverage for the wide range of variants.
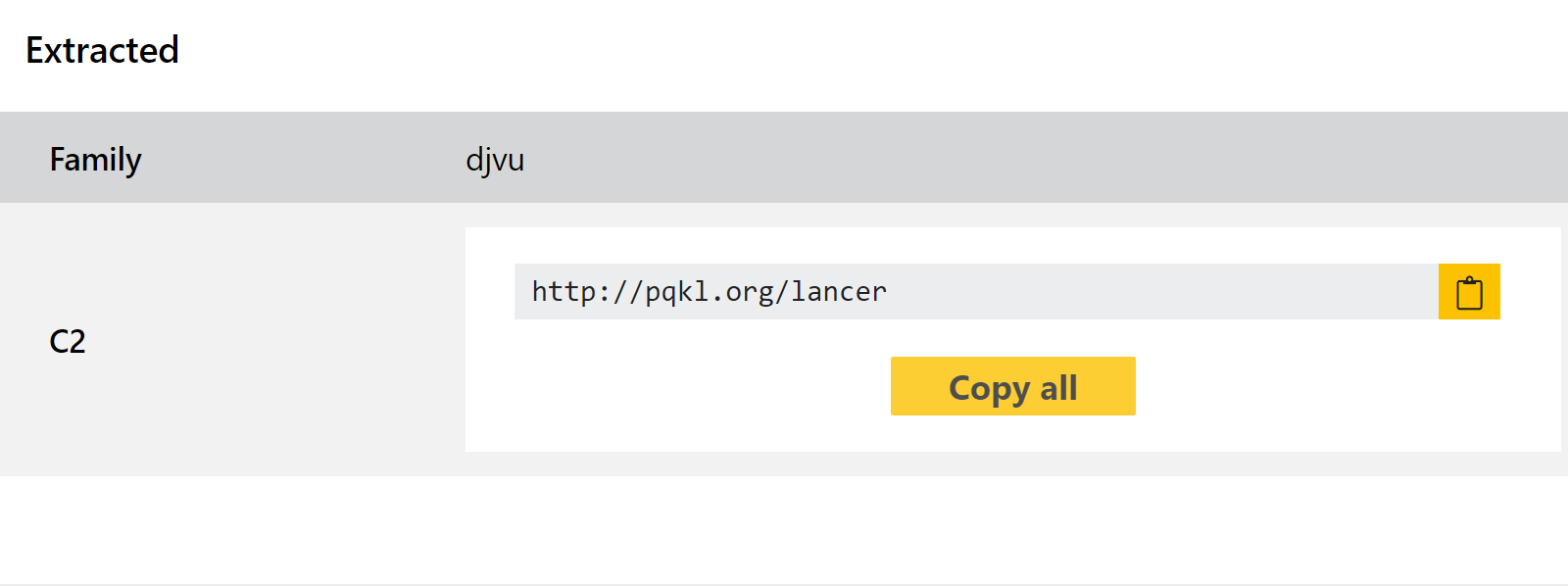
For those not already familiar with the family, DJVU was first reported in December 2018. Only around a year later Emsisoft reported that the family included 160 variants with a confirmed total of around 116,000 victims globally.
The family itself is a variant of the STOP ransomware. Early versions were poorly made, allowing many victims to decrypt their files without paying a ransom. Emsisoft also published a decryptor in late 2019 which had good coverage of versions up to that time, but since then the creators have tightened up the encryption methods to prevent bypasses.
We have reprocessed recent DJVU samples which you can find via Search. We have also listed a few examples below for reference.
Analyses:
NGLite RAT
NGLite is an open source Chinese-language RAT. The first version was published on Github in May 2021, with an update adding more functionality appearing in July.
As usual with these open source projects it presents itself as a legitimate remote administration tool, but a quick look at the Readme makes the intentions clear with features such as anonymity and techniques to prevent the program being terminated on a host being prominently promoted.
It seems that a major use-case for the malware is in the manual exfiltration of data from a network rather than acting as an automated stealer. It boasts of the capability to handle large file transmissions at high speed due to its network architecture, and appears to include few of the other features commonly seen in these applications to automate more general data collection.
We have observed a few samples appearing on Triage lately, so the team has taken a look and implemented detections for the family. You can find examples of the payload linked below.
Analyses:
Vidar Stealer
Vidar is a successful infostealer which was initially forked from the older Arkei stealer codebase. We have covered the family a few times on this blog recently so won’t go into detail on the background again here - you can find further information in our previous blogposts where we initially added a configuration extractor and then updated it for additional samples.
We recently observed some samples on Triage which were making use of new web services for their C2 communications, the details of which were not being properly dumped by our extractor. These are both Mastodon instances, available online as social communities:
- Koyu[.]space, a small social media site trying to position itself as a free-speech alternative to the likes of Twitter
- social[.]chinwag[.]org, a small online community that has been operating since around 2017
We have now tweaked the extractor to also dump the relevant domains and URLs being used for these services.
Analyses:
- 211108-xpsfqschd6 (koyu.space)
- 211108-x56cjaaafk (social.chinwag.org)
CobaltStrike
CobaltStrike has been a regular visitor to this blog over the last couple of years, as we’ve implemented a range of detections and configuration extraction tweaks to ensure the framework is handled as well as possible by Triage. This week we have revisited it with a minor update to address some false-positives that were reported to us. If you’ve been noticing files incorrectly identified, the signature should now be more reliable on that front.
Analysis:
