So far Triage has featured relatively minimal processing of network-based data from analyses. This week that is starting to change, with the initial release of SMTP and FTP extraction functionality. You can see the new change in action on the following examples:
- 200506-5pd5sx2aze (Hawkeye Reborn)
- 200506-8b7wef4dwe (AgentTesla)
This is the first in a planned series of expansions to the current network handling. Watch this space for more updates!
SMTP/FTP in Malware
Malware can use any number of methods to implement C2 communications, with SMTP (Simple Mail Transfer Protocol) and FTP (File Transfer Protocol) being no exception. These are popular protocols to evade common monitoring/filtering efforts as there are many legitimate uses for these technologies in any corporate (or home) network, and separating legitimate use from malicious can be resource intensive and slow at scale.
Some examples of families which use these protocols are:
| SMTP | FTP |
|---|---|
| AgentTesla | FIN8 Group |
| Lazarus Group | HawkEye |
Automatic packet dumping and decryption
With the new functionality now on Triage, any SMTP or FTP traffic will be detected and processed to:
- Parse connection info - hostname, port number etc.
- Decrypt the stream if necessary (i.e., uses TLS)
- Extract any SMTP/FTP login credentials submitted by the sample.
The results of this processing are stored in the JSON report (report_triage.json) with the following layout:
"extracted": [
{
"credentials": {
"protocol": "smtp",
"host": "smtp.yandex.ru",
"port": 587,
"username": "[email protected]",
"password": "kingmoney12345"
}
}
This data is rendered in the web UI under the Malware Configuration section as shown here:
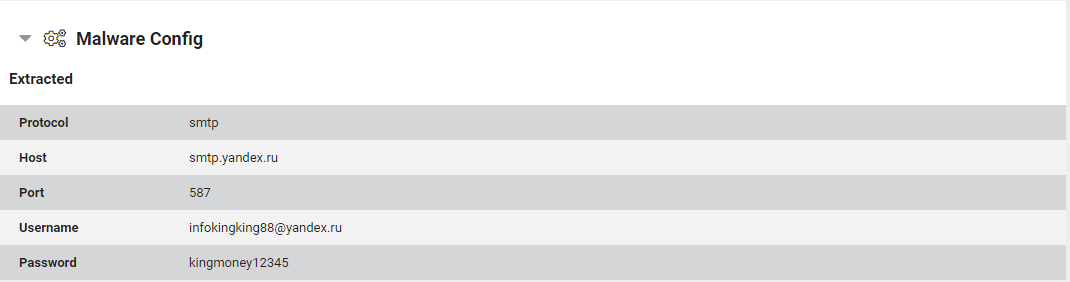
Example extracted SMTP Credentials in the UI
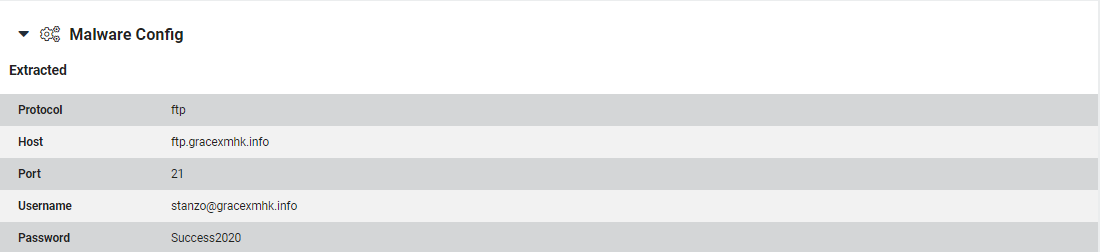
Example extracted FTP Credentials in the UI
Conclusion
We hope that this feature will be a useful addition to Triage™ analyses. If you have any feedback about this or other features - or just want to report a sample not working as expected - feel free to get in touch with us using the details at the bottom of the page. Follow us on Twitter (@hatching_io) for news on the latest changes as they are released.
Not signed up yet? Head on over to https://tria.ge/ to request early access to the platform!
